Cybersecurity threats present a challenge to the normal functioning of critical infrastructure both nationally and globally. Staying up to date on cybersecurity best practices and taking proactive steps to prevent breaches can help your company avoid incidents or at least minimize their impact.
At Trane, we align our approach to cybersecurity with National Institute of Standards and Technology’s (NIST®) “Framework for Improving Critical Infrastructure Cybersecurity.” Although every company and industry is different, following these general guidelines and steps can help your organization better position itself to prevent or recover from cyberattacks.
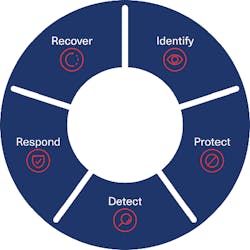
5 steps to improving organizational cybersecurity.
Identify: Identify all the assets in your building (building automation system/IoT devices equipped in the network). Assess your risks. Understand your organizations cybersecurity strengths and weaknesses. Identify where risks and opportunities to improve may lie.
Protect: Proactively act on your assessment and provide protection for your assets. Implement safeguards to reduce risks such as preventative procedures, equipment/technology updates, staff training, etc.
Detect: Enact activities such as continuous asset and network monitoring to detect the occurrence of cybersecurity events as early as possible.
Respond: Develop a set of response planning and mitigation strategies. These might include efforts to contain or minimize impact, analysis, and assessment of the incident and its impact on the organization.
Recover: Outline recovery processes, business continuity procedures and best practices to help ensure timely restoration of building systems or assets affected by cybersecurity events to return to normal operation as quickly as possible.
For more information, read the NIST Framework here.
In addition to improving the framework for your business, there are solutions that can be employed to mitigate the risk. These next steps focus on what can be collectively done to address the challenges of cybersecurity within building automation systems.
Teaming: Proactive communication with IT & Facility Managers is essential to address bridging the gap. Project specifications drive product requirements, installation, best practices, and maintenance. Clearly communicate the benefit of the asks, use standard terminology and diagrams, utilize proper protocols and technology, and cue in facility managers to help ensure sustainable solutions.
Secure Product: A secure product is the foundation for a securely deployed building automation system. Cybersecurity features are complex—out-of-the-box-solutions can reduce common application mistakes while simplifying IT engagement and maintenance.
Secure Installation: Secure products aren’t enough, secure installation practices are required. These best practices must address installation process, user management, etc. This can include restricting physical controller access, isolating controls from other network devices (VLAN/Firewall), ensuring secure user credentials aren’t shared, having a well-documented process and owner to keep system up to date, and more.
Maintenance: Specifications and contract terms must drive a clear understanding of controller life cycles, planning for scheduled and unscheduled updates, and implementing appropriate system maintenance intervals. Ownership for risk mitigation is paramount, software vulnerabilities are a reality and diligence is required to address them promptly.
Learn more about Trane’s approach to Cybersecurity at Trane.com.
Sponsored by: